
One of the main features of cryptocurrencies, as per their proponents, is security.
According to them, breaking into your crypto wallet is impossible, and crypto offers a level of security no bank ever has or will.
Yet cryptocurrency gets stolen anyway.
Not only does it get stolen, but generally, quantities stolen amount to millions.
So which one is true? Are cryptocurrencies secure or not? That’s a complex answer. Cryptocurrencies are secure by design.
Nobody can access your wallet without your permission, and stealing somebody’s crypto wallet is worthless since you’ll be unable to access it.
That doesn’t mean there are no ways to access it, though. Generally, however, people stealing crypto don’t hold you at gunpoint and ask for your precious Bitcoin.
Instead, they attack apps or sites you trust, or masquerade as useful, perfectly clean services.
1.They target crypto exchanges
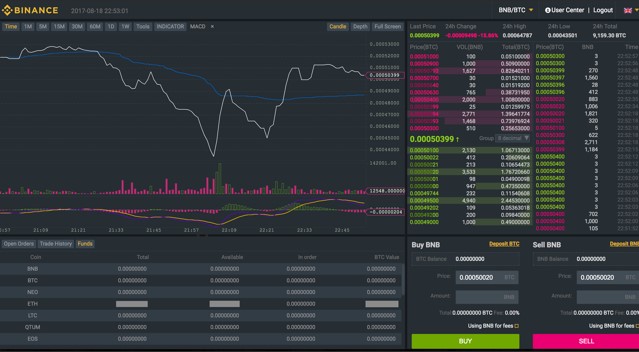
Individual theft of cryptocurrency happens. However, the most common way for cryptocurrency thieves to obtain your hard-earned crypto is by hacking into exchange sites.
Crypto exchange sites operate in particular ways, since they allow you to have a wallet with them where you can deposit and exchange currencies.
Therefore, you could think of these sites as huge crypto banks.
Since bank robbing has been the pastime for thieves for centuries, you’ll understand why this attracts them.
Generally, these hacks take a long time. A hacker will identify a vulnerability in the website’s code or functioning and use it to slowly gain access to user accounts.
Once he has it, he has to just transfer money to his account and run off with it.
TIP: Don’t leave crypto lying around in exchange sites. You want a private wallet to hold whatever crypto you’re saving, and you want to have it away from the internet.
The only money you must have in crypto exchanges is money you’re using or going to use soon.
2.They log your keys
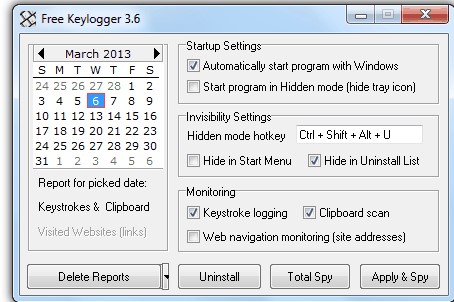
Many people think spyware is a very 2004 thing. We have come a long way regarding computer security, with most systems coming with built-in anti-spyware, anti-keylogger features.
They’re basically parts of anti viruses now, so we should be able to do as we want, and the system should catch anything wrong.
Except that it won’t catch anything!
The way antiviruses or antispyware systems work is simple: They scan your system for known malware.
They have huge databases of how to identify and remove malware and go through it as they perform a scan. That’s about it.
Some have also extra features allowing them to scan running processes, trying to catch suspicious activity or programs attempting to gain permissions they don’t have.
So if a keylogger tries to run without your permission, they should catch it and-
We only wish it were that simple. In most cases, keyloggers come disguised as other software. When you install that software, they ask for permissions, and you happily grant them.
Your local antimalware sees it, but it notices it has your permission and the software isn’t in their database (yet.) So it lets it through.
And that’s how you get your keys logged. Once they log your keys, it’s simple for them to obtain your private key, access the blockchain as you, and do some good old stealing.
TIP: Don’t install things you can’t trust. Assume you can’t trust anything unless there’s enough proof of the opposite.
3.They go Trojan

Remember about the Trojan horse? How Troy was invaded by a bunch of men inside a huge horse the Trojans let in?
The same thing can happen in computers. Not every software is what it
seems. Particularly if that software is meant to handle sensitive data.
What this means is, some people will code software that looks like something genuine while instead doing something else. Sometimes the software will even do what it says it does… and a million other things.
In cryptocurrencies, it’s common for hackers to code amazing new wallets.
They come with offers and promise lots of things. They seem better than anything out there, and many times they work at first.
Until one day the hacker grabs all those private keys users stored in those wallets and uses them to rob them blind.
This type of hack with fake wallets is more common in Android and other mobile devices, but it can happen anywhere.
TIP: Don’t install new, “amazing” wallets. If it looks too good to be true, it’s probably very good at stealing your crypto. Only trust wallets the community has reviewed extensively.
Conclusion
The Internet age came with lots of convenience as well as severe threats. Same goes with the era of the blockchain.
Hackers roam the cyberspace always, looking for whom to devour.
As a crypto trader, stay alert always, and you will keep hackers at bay.

